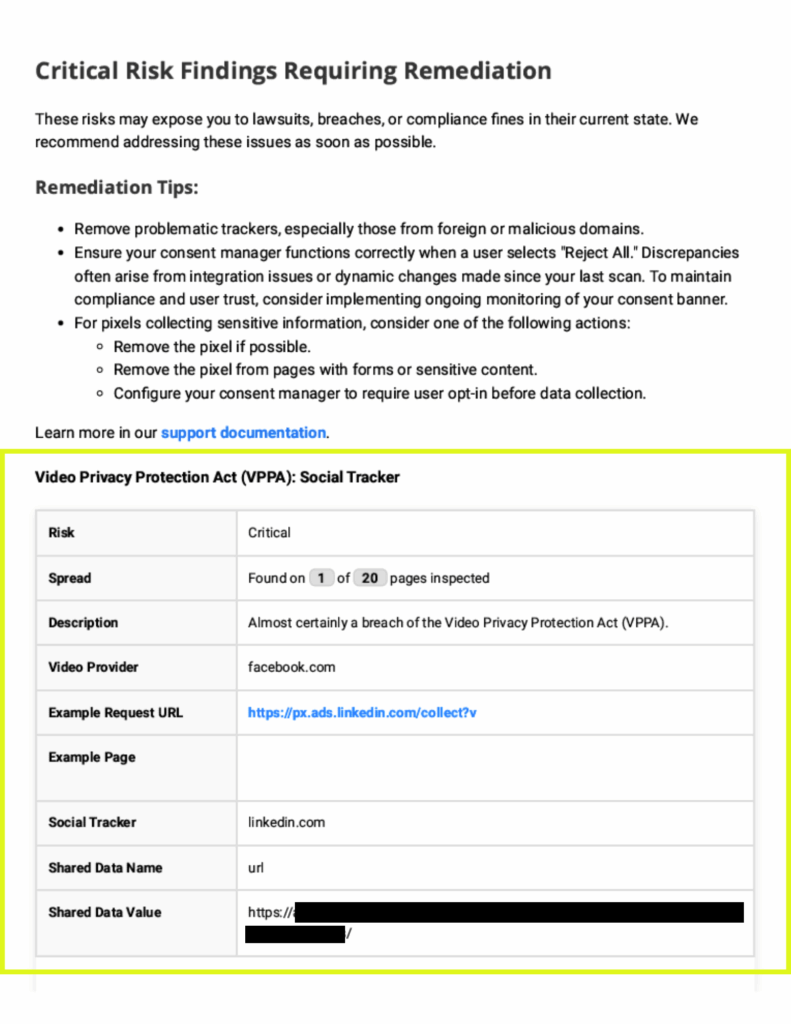
First-party cookie risk
This category also includes first party cookies that were set before or without obtaining explicit user consent. First-party cookies are generally intended for website use, while third-party cookies are for use by third parties. However, a JavaScript workaround exists that allows third parties to set first-party cookies, creating first-party cookie risk.